Share your love
Secure Apache with Let’s Encrypt on AlmaLinux 9

This tutorial on the Orcacore website intends to teach you How To Secure Apache with Let’s Encrypt on AlmaLinux 9. Apache is the most commonly used Web server on Linux systems. Web servers are used to serve Web pages requested by client computers. Let’s Encrypt is a free certificate authority developed by the Internet Security Research Group (ISRG).
Let’s Encrypt provides two types of certificates. The standard single-domain SSL and the Wildcard SSL cover not only a single domain but all of its subdomains too. Both types of SSL certificates are issued for 90 days, and on SiteGround servers, when installed, they are renewed automatically.
These certificates are domain-validated, don’t require a dedicated IP, and are supported on all SiteGround hosting solutions.
Table of Contents
Steps To Secure Apache with Let’s Encrypt on AlmaLinux 9
To secure your Apache web server with Let’s Encrypt, you need to meet some requirements.
First, you need to log in to your server as a non-root user with sudo privileges and set up a basic firewall. To do this, you can follow our article on the Initial Server Setup with AlmaLinux 9.
Also, you need to have Apache installed on your server. For this, you can check our guide on How to Install an Apache Web server on AlmaLinux 9.
At this point, follow the steps below to Secure Apache with Let’s Encrypt on AlmaLinux 9.
1. Install Certbot on AlmaLinux 9
First, you need to install the EPEL repository and the mod_ssl package, which is a security module for the Apache HTTP server that provides strong cryptography by leveraging SSL/TLS protocols using OpenSSL:
sudo dnf install epel-release mod_ssl -yThen, install “certbot” to get an SSL certificate with Let’s Encrypt on AlmaLinux 9 with the command below:
sudo dnf install certbot python3-certbot-apache -yAt this point, certbot is installed on your server. Let’s get an SSL certificate for your domain name.
2. Get an SSL Certificate from Let’s Encrypt for Apache
At this point, you can get your SSL certificate with Let’s Encrypt by following these steps:
sudo certbot --apacheIt will ask you some questions. The first will ask you to enter your email address for renewal notifications and security notices:
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Enter email address (used for urgent renewal and security notices)
(Enter 'c' to cancel): sam@orcacore.com
...After entering your email address, press Enter to proceed to the next step. You will be asked to confirm if you agree to Let’s Encrypt’s terms of service.
Please read the Terms of Service at
https://letsencrypt.org/documents/LE-SA-v1.3-September-21-2022.pdf. You must
agree in order to register with the ACME server. Do you agree?
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
(Y)es/(N)o: Y
...At this point, you will be asked to share your email address with the Electronic Frontier Foundation.
Press ‘N’ to continue, if you want to receive the information, type ‘Y’.
Would you be willing, once your first certificate is successfully issued, to
share your email address with the Electronic Frontier Foundation, a founding
partner of the Let's Encrypt project and the non-profit organization that
develops Certbot? We'd like to send you email about our work encrypting the web,
EFF news, campaigns, and ways to support digital freedom.
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
(Y)es/(N)o: N
Account registered.
...At this point, it is important to set up your virtual hostname at the beginning of the article. Enter the domains you want to activate HTTPS for.
Please enter the domain name(s) you would like on your certificate (comma and/or
space separated) (Enter 'c' to cancel): example.com
Requesting a certificate for example.com
...At this point, the certbot configuration is finished. And you will see this in your output:

Your certificate with Let’s Encrypt on AlmaLinux 9 is now installed and loaded into Apache’s configuration.
Type your domain name in your web browser, you will see the lock icon in the address bar.
At this point, you can use the SSL Labs server test to verify your certificate from Let’s Encrypt too. You can go to the page and enter your hostname there.
3. Set up Auto-Renewal Of Let’s Encrypt Certifications
In this step, you have learned how to secure Apache with Let’s Encrypt on AlmaLinux 9 and configure it.
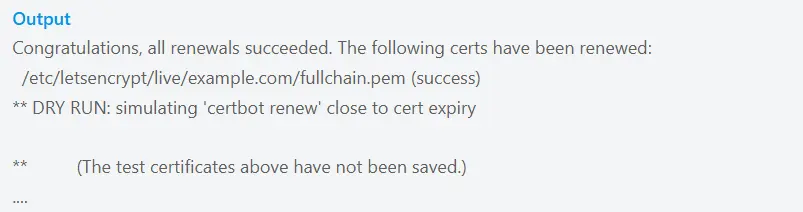
At this point, you should know that Let’s Encrypt certificates are valid for 90 days, but it’s better to renew them every 60 days automatically. To do this, run the command below:
sudo certbot renew --dry-runYou will see this in your output:
Conclusion
At this point, you have learned to secure Apache on AlmaLinux 9 with Let’s Encrypt to enable free SSL/TLS for HTTPS access. It boosts security, trust, and SEO by encrypting traffic between your server and users.
Hope you enjoy it. Please subscribe to us on Facebook, X, and YouTube.
Also, you may like to read the following articles:
Set up Nginx with Let’s Encrypt on AlmaLinux 9