Share your love
Install Wireshark on AlmaLinux 9: Best Network Packet Capture
In this guide, you will learn to Install Wireshark on AlmaLinux 9. Few tools are as useful to the IT professional as Wireshark, the go-to network packet capture tool. Wireshark will help you capture network packets and display them at a granular level. Once these packets are broken down, you can use them for real-time or offline analysis. This tool lets you put your network traffic under a microscope, and then filter and drill down into it, zooming in on the root cause of problems, assisting with network analysis and ultimately network security.
Now follow the guide steps on the Orcacore website to Install Wireshark on AlmaLinux 9.
Table of Contents
Steps To Install Wireshark on AlmaLinux 9
To complete this guide, you must log in to your server as a non-root user with sudo privileges. To do this, you can follow our guide on Initial Server Server Setup with AlmaLinux 9.
Installation Steps of Wireshark on AlmaLinux 9
By default, Wireshark packages are available in the default AlmaLinux 9 repository.
First, update your local package index with the following command:
sudo dnf update -yThen, use the following command to install the Wireshark GUI App on your server:
sudo dnf install wireshark -yGet Wireshark CLI
If you do not have GUI/Desktop installed you can install and use Wireshark as a command line tool. To do this, run the command below:
sudo dnf install wireshark-cli -yLaunch Wireshark
You can now launch Wireshark either from the command line or from the activities. To start Wireshark, run the following command:
sudo wireshark &You will see the Wireshark interface on AlmaLinux 9:
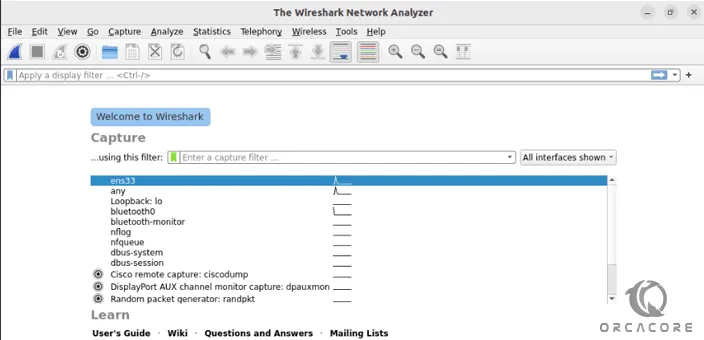
Now you can start using your Wireshark. For example, you can Capture the data from available network interfaces. To do this, click on the shark flipper icon in the top left corner to start recording.
In case you wish to use the Wireshark CLI commands use the following command:
tshark --helpOutput
Usage: tshark [options] ...
Capture interface:
-i <interface> name or idx of interface (def: first non-loopback)
-f <capture filter> packet filter in libpcap filter syntax
-s <snaplen> packet snapshot length (def: appropriate maximum)
-p don't capture in promiscuous mode
-I capture in monitor mode, if available
-B <buffer size> size of kernel buffer (def: 2MB)
-y <link type> link layer type (def: first appropriate)
--time-stamp-type <type> timestamp method for interface
-D print list of interfaces and exit
-L print list of link-layer types of iface and exit
--list-time-stamp-types print list of timestamp types for iface and exit
Capture stop conditions:
-c <packet count> stop after n packets (def: infinite)
-a <autostop cond.> ... duration:NUM - stop after NUM seconds
filesize:NUM - stop this file after NUM KB
files:NUM - stop after NUM files
Capture output:
-b <ringbuffer opt.> ... duration:NUM - switch to next file after NUM secs
interval:NUM - create time intervals of NUM secs
filesize:NUM - switch to next file after NUM KB
files:NUM - ringbuffer: replace after NUM files
Input file:
-r <infile> set the filename to read from (- to read from stdin)
Processing:
-2 perform a two-pass analysis
-M <packet count> perform session auto reset
-R <read filter> packet Read filter in Wireshark display filter syntax
(requires -2)
-Y <display filter> packet displaY filter in Wireshark display filter
syntax
-n disable all name resolutions (def: all enabled)
-N <name resolve flags> enable specific name resolution(s): "mnNtdv"
-d <layer_type>==<selector>,<decode_as_protocol> ...
"Decode As", see the man page for details
Example: tcp.port==8888,http
-H <hosts file> read a list of entries from a hosts file, which will
then be written to a capture file. (Implies -W n)
--enable-protocol <proto_name>
enable dissection of proto_name
--disable-protocol <proto_name>
disable dissection of proto_name
--enable-heuristic <short_name>
...For more information, you can visit the Wireshark Documentation page.
Conclusion
At this point, you have learned to Install Wireshark on AlmaLinux 9 and easily get Wireshark CLI commands. With Wireshark, you can easily capture network packets and display them at a granular level.
Hope you enjoy it. You may like these articles: